I installed a root CA on my iPhone and intercepted my own traffic on my firewall using Squid. Here’s a look at what your favourite apps call behind your back.
Official Apple apps
Phone app
It made calls to my mail server (presumably to fetch contacts).
Mail (with two on-prem Exchange accounts)
Called my Exchange servers only.
Camera
No traffic.
(Apple) Maps
Lots of calls to https://gspe19-ssl.ls.apple.com/asset/v3/material/
App Store
Detected TLS inspection, so it’s using pinned certs. ‘Something went wrong’.
Social networks
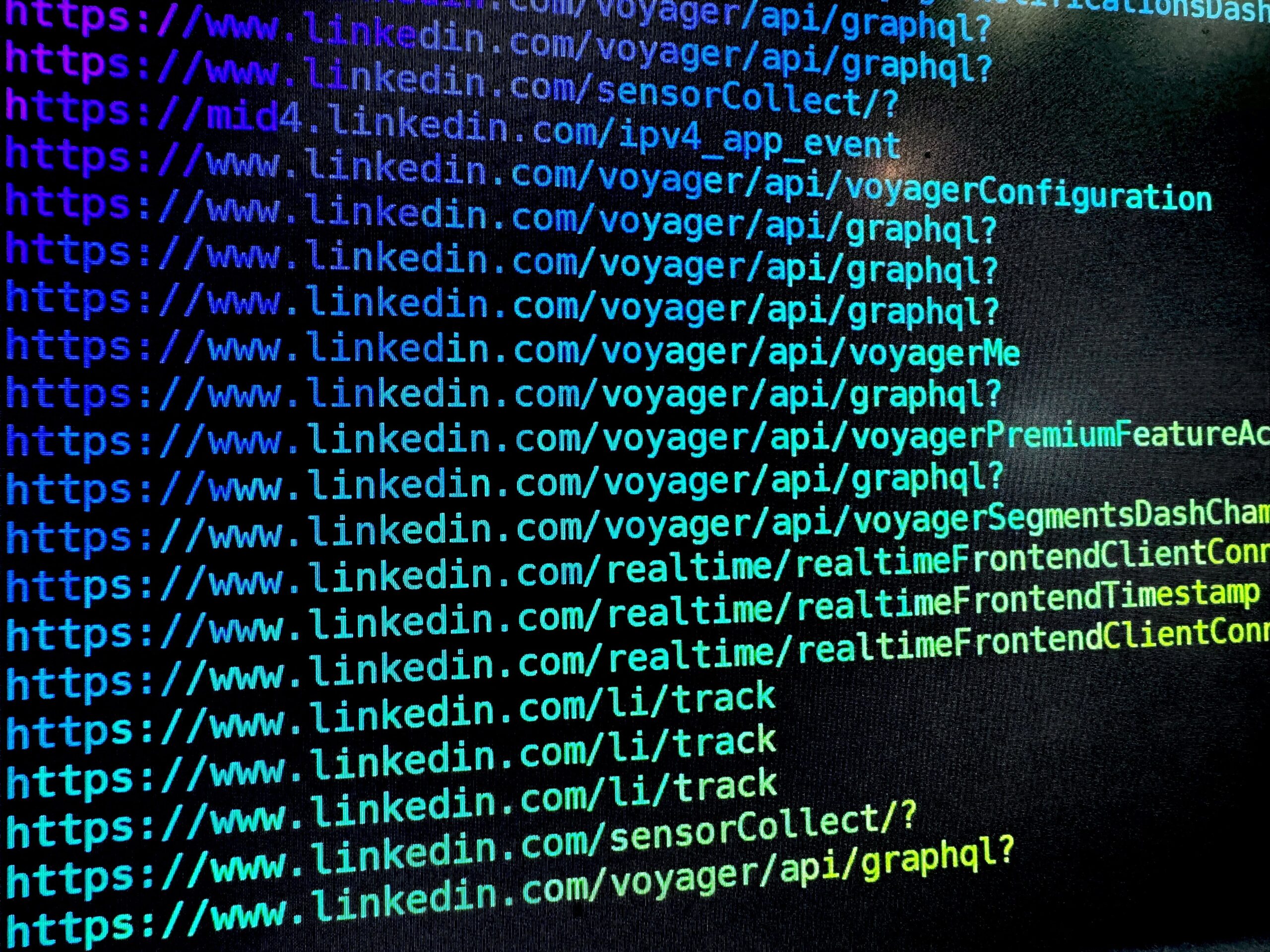
LinkedIn primarily uses GraphQL for most API calls, and there is a tracking endpoint frequently called at https://www.linkedin.com/li/track. I also found a “whoami” style endpoint at https://www.linkedin.com/mob/sso/you. A media CDN at media.licdn.com appears to be doing authentication correctly.
When I turned off DNS-based ad blocking, a little bit more is called, such as https://gsp10-ssl.apple.com/hvr/trc which seems to be an Apple tracking server. I also saw calls to api.mapbox.com.
X/Twitter
Nothing too weird. Seems to be mostly the same stuff you’d see on desktop:
https://video.twimg.comhttps://abs.twimg.comhttps://pbs.twimg.comhttp://connectivitycheck.gstatic.com(this one is Google’s network)
Weird one – it doesn’t seem to make calls to hostnames, instead calling a few IPs on port 443 on ASN 32934 (FACEBOOK).
Generally was very quiet. Some calls to Facebook, such as whatsapp-cdn-shv-01-lhr6.fbcdn.net.
Signal
Some calls to AWS.
Security / sysadmin apps
Authy
It made calls to the following endpoints:
https://kinesis.us-east-1.amazonaws.com/https://api.authy.com/- a few other IPs
RD client (Microsoft RDP)
No unexpected traffic.
Terminus
No unexpected traffic.
Self-hosting community favourites
Bitwarden (self-hosted server)
I saw no calls to the Internet 🙂
Nextcloud
Nothing at all hitting the Internet.
Mastodon (not logged in)
No traffic.
Media
Spotify
Very noisy. Some common calls:
https://audio-ak-spotify-com.akamaized.net/https://canvaz.scdn.co/https://firebaseinstallations.googleapis.com/https://i.scdn.co/https://api-adservices.apple.com/api/v1/
Travel
Airbnb
- A few calls to their API
https://www.airbnb.com/tracking(presumably analytics)https://firebaseinstallations.googleapis.com/v1/projects/airbnb-38fb0https://a0.muscache.com/im/pictures/
Google Maps
As expected, a major offender:
https://mobilemaps.googleapis.com/maps/vt/protohttps://play.googleapis.com/log/batchhttps://scone-pa.googleapis.com/v1/survey/triggerhttps://oauthaccountmanager.googleapis.com/v1/issuetokenhttps://www.googleapis.com/userlocation/v1https://gz0.googleusercontent.com/https://www.gstatic.com/identityhttps://fonts.gstatic.com/s/roboto/https://accountsettingsmobile-pa.googleapis.com
Tesla
Generally called its own stuff, but also DataDog and Google.
https://owner-api.teslamotors.com/api/1https://signaling.vn.teslamotors.com/v1/mobilehttps://browser-intake-datadoghq.com/api/v2/rumhttps://www.googleapis.com/experimentsandconfigs/v1
Uber
Hard to know – all calls went to CloudFront.
Requests…
If you’d like me to decrypt another app, contact me and I’ll update this post. If you’re a developer and think I got something wrong here, let me know and I’ll take a look.